A click is the prominent way that users interact with content on the World Wide Web (WWW). Malicious third-party advertisers or hackers expose web users to a security threat by injecting malicious JavaScript code to intercept user clicks and trick them into visiting untrusted web content. Attackers aim to intercept genuine user clicks to either launch ad click frauds by fabricating ad click traffic, or to send malicious commands to another website on behalf of the user (e.g., to force the user to download malwares). This project developed a browser-based analysis framework – Observer, which is able to detect three different techniques for intercepting web user clicks. Different from previous researches that mainly considered the type of click interceptions launched by malicious first-party websites, Observer addresses this research gap, in which it considers the various click interceptions launched by third-party JavaScript code.
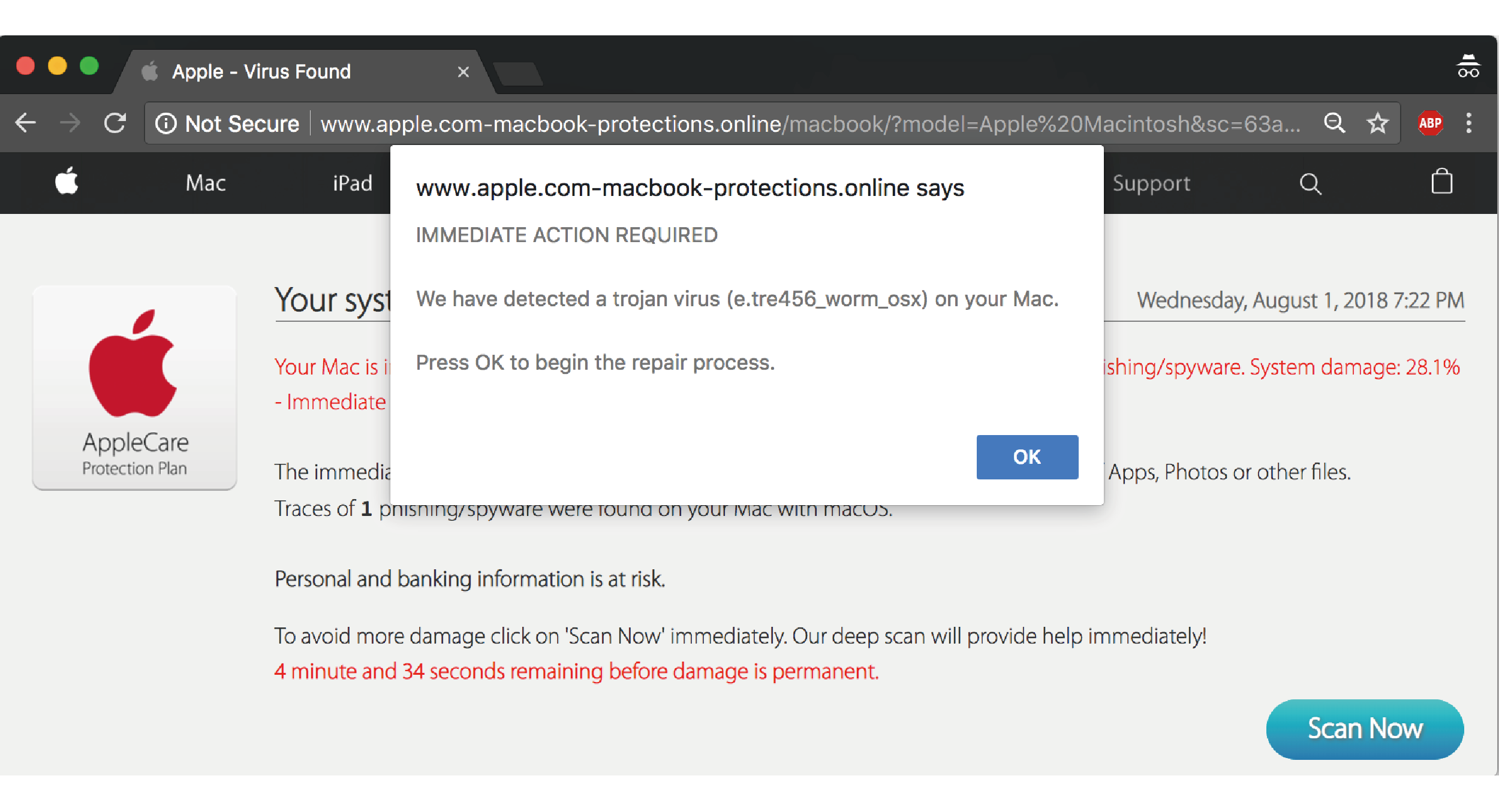
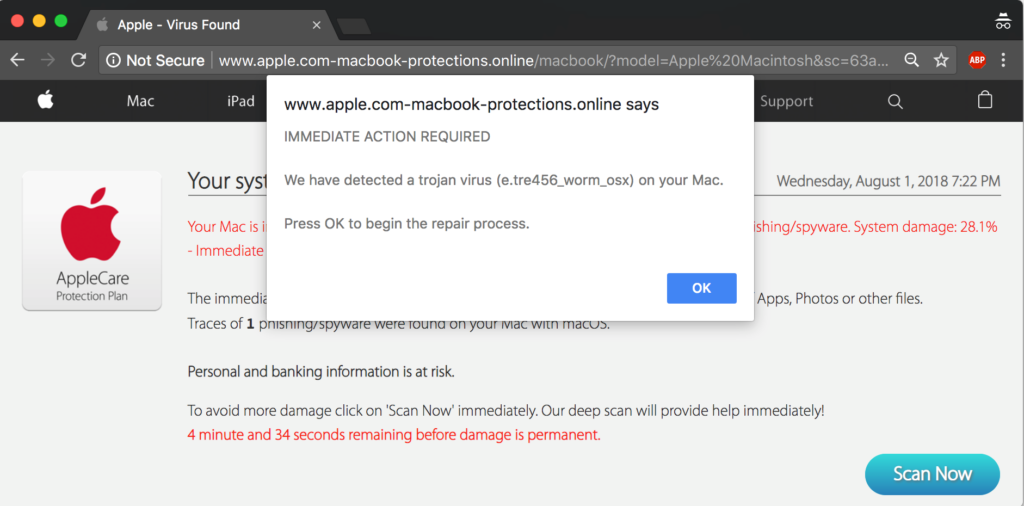
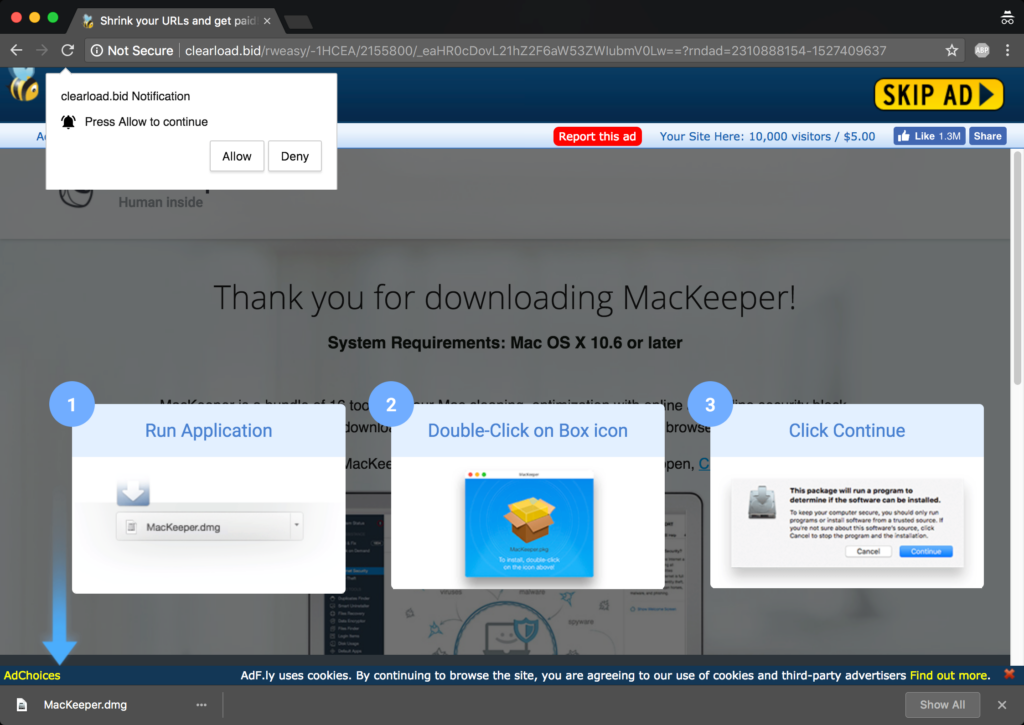
It is acknowledged that web behaviour caused by third-party JavaScript code is difficult to record and analyse. Observer detects third-party click interceptions by extending the browser to collect the behaviour at runtime and thoroughly analysing the click-related behaviour. Using Observer, we analysed Alexa top 250K websites, and detected 437 third-party scripts that intercept user clicks on 613 popular websites, which in total receive around 43 million visits on a daily basis. In particular, though click interception, these scripts could trick users into visiting 3,251 untrusted unique uniform resource locators (URLs) controlled by third parties. Over 36% of them were related to online advertising. Further, some click interception URLs led users to malicious content such as scamwares. This demonstrates that click interception has become an emerging threat to web users. Our research team has released the source code of the framework publicly to help web browsers detect malicious click interceptions and alert users about the malicious behaviour to protect them from being exposed to malicious content.
The research identified three categories of click interception techniques:
- Modifying the destination URL of hyperlinks to lead users to malicious websites upon clicks.
- Adding click event listeners to manipulate user clicks.
- Visual deception, for example, by creating web content that is visually similar to first-party content, or displaying transparent elements on top of the web page. The former will trick users into clicking third-party element, and the latter enables the transparent elements to capture all user clicks on first-party content. Consequently, the users can be led to a page controlled by the attackers.